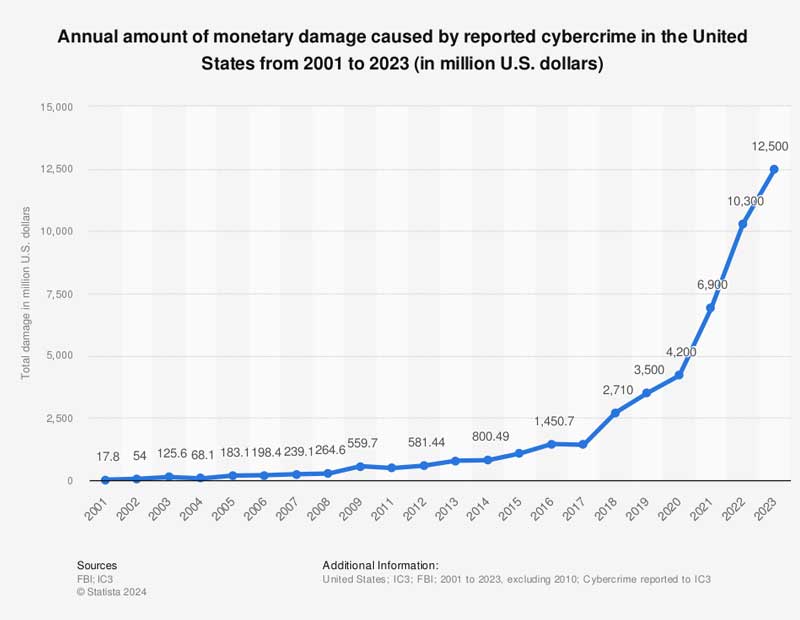
Together with the on a regular basis challenges that property managers face, cybercrime poses a rising risk. Final yr alone, this situation was answerable for $12.5 billion in harm to the U.S. financial system. As industrial actual property stakeholders undertake extra expertise, their vulnerability to knowledge theft, ransomware and property harm has elevated.
Property managers are on the entrance traces of stopping intrusions, and, at occasions, mitigating their impression.
Avenues of assault
A part of the complexity of shoring up industrial actual property cybersecurity lies within the variety of targets and assault vectors. Ransomware assaults, that are growing in frequency and price, can hit industrial actual property’s huge amount of native and externally hosted monetary knowledge. Something from social engineering makes an attempt to passwords offered on the darkish internet can simply entry this info.
Add to this the truth that stakeholders at workplace and industrial properties typically have their very own individually managed tech stacks, entry management applications and web of things-connected constructing sensors. The result’s no scarcity of alternatives for knowledge theft and system-wide disruptions.
Workplace buildings face larger dangers on account of “intensive networks and quite a few related gadgets,” in line with Chris Barns, vp at R&Okay Options. Industrial buildings, with their digitized mechanical and management methods, are topic to dangers to individuals and property. Within the retail sector, bank card fraud typically serving as a lever for ransomware attackers, in line with Barns.
Even refined buyers don’t essentially have all of the protection they want on this space. “Institutional buyers who run pension funds … will in all probability have a cyber coverage that covers its staff, knowledge utilization and all the things,” famous Nick Wright, international head of digital options at CBRE Property Administration. “What we’re discovering is that they don’t have a cyber coverage that pertains to the property they personal or put money into.”
READ ALSO: Finest Practices for AI and Knowledge Integration: CRE Leaders Weigh In
This all occurs as attackers are getting extra refined, whereas knowledge stewards have seen their vulnerabilities multiply. In keeping with John Worth, founding father of SubRosa Cyber, a cybersecurity consulting agency with a give attention to industrial actual property, attackers are solely getting extra artistic, significantly within the phishing realm. They are actually even utilizing free trials of DocuSign to grab useful consumer knowledge.
For Worth, this predicament is made worse as a result of many house owners and property managers have satellite tv for pc workplaces with direct entry to mainframes. In concept, a hacker attacking a small satellite tv for pc workplace can get all the best way to company headquarters.
The growing presence of automation and web of things-connected sensors provides to the recipe for bother. “You open up your methods for disruption by simply making so many entry factors into your community,” Barns mentioned.

The outcomes? “They’ll stop to function on the industrial facet, and on the commercial facet of issues, they’re inclined to a software program takeover that may have an effect on extra than simply the gadgets themselves,” Worth instructed Business Property Govt.
If a ransom is just not paid, the consequences can vary from lack of delicate knowledge to gear sabotage that endangers lives and property.
Final yr, Clorox suffered a ransomware assault that took almost all of its automated methods offline. In 2021, Colonial Pipeline suffered an assault from Russian hacking group DarkSide on its billing infrastructure which affected management methods. This hack, in flip, triggered gasoline shortages throughout the Japanese Seaboard
And attackers might have motives that transcend a ransom. It’s all too simple to think about an adversary sabotaging the SCADA or HVAC methods at a chemical or pharmaceutical manufacturing plant in a time of battle. “Any compromised methods might endanger the protection of the tenants inside these buildings,” Barns cautioned.
What’s on the root of dangers
However this numerous array of vulnerabilities normally stems from the identical root trigger. “The weakest hyperlink within the safety chain is just not expertise or infrastructure, however individuals,” mentioned Chuck Briese, vp of data safety at Transwestern. “Ninety p.c of breaches are nonetheless being created by phishing.”

However even out-of-the-box cybersecurity software program can have unintentional weak spots. “Typically the software program or passwords are very low safety and are fairly simple to crack and get into,” in line with Worth. The 2020 SolarWinds assault, which penetrated the networks of hundreds of corporations and authorities businesses worldwide, was executed partially on account of an unchanged default password: SolarWinds123.
In Briese’s expertise, negligent cyber hygiene exists within the {hardware} realm, as nicely. “A few of these buildings that (we handle) are 30 to 40 years outdated and have handed via myriad property administration corporations,” he mentioned. “They’ll inform us what they assume they know, however they don’t notice that there’s a 10-year-old, 4-port Netgear change someplace within the ceiling that’s passing visitors to unknown locations.” Upon assuming administration duties at a property, Briese’s group will typically discover a PC that’s turned on and plugged into the community. The state of affairs is dropped at the group’s consideration via community scanning.
What’s extra, exterior distributors have entry to safety methods, HVAC methods and the like, and supportive work is usually accomplished via a port that passes a firewall and forwarded straight right into a system. “(It’s) extremely insecure, as a result of we’re opening up that port within the firewall for anyone,” Briese noticed.
However typically even a firewall is a luxurious. Wright, discussing factors of contact for remotely accessed applied sciences, discovered “that entry is on an open IP deal with,” virtually holding the door open for a saboteur.
Finest practices for preparation
In an excellent world, an oz. of cybersecurity prevention is value a pound of treatment. Usually, the best options are the simplest. “The practices should be associated to the significance of guaranteeing that passwords are up to date, knowledge is saved in the appropriate place, software program updates are accomplished in time and recorded,” Wright noticed.
For third-party entry management, Briese advises utilizing a VPN, to make it more durable for hackers to steal knowledge. Even when they will get in, implementing a zero-trust safety mannequin makes it prohibitively tough for a breach to unfold, in line with Barns.
One other space that doesn’t all the time come to thoughts, even for cybersecurity-minded property managers, is vendor choice. “Making certain that these distributors have an excellent cybersecurity course of in place to mitigate dangers might be one of many high priorities when investigating which vendor to go along with,” Barns suggested.
On the logistics entrance, Barns sees each a direct and third-party analysis of methods as a useful but typically neglected protocol. A extra goal evaluation cannot solely assist patch identified factors of vulnerability, however routers on the portfolio degree. “For those who don’t know all the property that you’ve on web site, it’s actually laborious to handle them and hold them safe,” Barns identified.
Worth advises managers who’re updating worker coaching protocols to account for the most recent threats. Concerning the format of coaching periods, Worth advises assembly with smaller teams as soon as a month for 15 to half-hour to assist make info extra digestible and present.

For mitigation, high of thoughts needs to be guaranteeing that breaches stay remoted to 1 machine or community, in order that an attacker can’t merely “pivot from a small regional property administration workplace to a company community,” in line with Worth.
Regardless that community segmentation could also be the secret, this course of is just not with out its difficulties, given the complexities related to managing properties and methods with a number of stakeholders.
As Wright put it: “If there have been a hack on a constructing right this moment, a bit of bit like your laptop computer, how do you turn it off and change it again on once more, going via that strategy of who these a number of stakeholders and subcontractors are?”
For that reason, backups of significant methods and knowledge are important, in addition to understanding that losses will include any hack, nonetheless minor. “You need to be sure you’re utilizing your newest backups to revive any of the affected methods in knowledge to get your methods again operational as rapidly as doable,” Barns suggested.
The reply lies within the fundamentals of cyber hygiene. “It’s nonetheless going to come back right down to the human parts,” Wright mentioned, “and that’s the greatest problem: ensuring that the individuals are doing what they’re meant to do.”
















